Why use Honeypot Protection

First of all, what is a honeypot?
Simply put, in the cryptocurrency realm, a honeypot represents a digital asset that can be bought but never sold.
More often than not, a honeypot is the attack vector of scammers, rug-pull actors and hackers trying to deploy various phishing scenarios in deceipting people to buy a specific ERC20 token in an attempt to steal their funds.
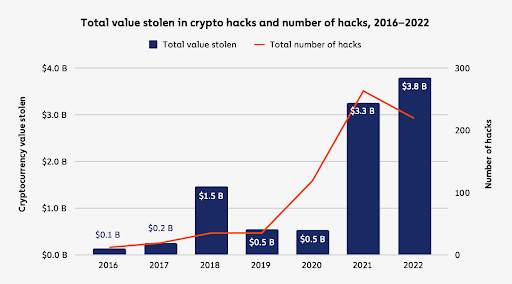
How risky is it?
The consequences of being a honeypot victim are as high as possible – it is equivalent to losing funds in a non-recoverable way. The reason why nothing can be done after such an attack is the fact that at that point – after buying such a malicious token – the attacker has complete control over your funds, and you’ll be left with a worthless token.
How can I protect myself ?
First of all, be very cautious about what is presented to you as “investment opportunities”, especially if you observe unnecessary pressure (time related, in most of the cases) to buy, trade or acquire a digital asset – be it native chain currency, token or NFT. Scammers and malicious actors are frequently using time pressure to create “fear of missing out” a.k.a FOMO, and to make their victims suspend their critical thinking.
While there are tools that can be used to perform security checks and due diligence, these are either too technical for most of the people or require expensive subscriptions that are prohibitive for majority of crypto users.
The good news is that OMNIA has integrated such tools directly in the RPC endpoints such that users don’t need to do anything too complex – they are protected by default against honeypot protection if they enabled these options with just a simple checkbox when generating their private endpoint.
Important: OMNIA’s public RPCs don’t have this option enabled by default.
If you want to enable honeypot protection, head to OMNIA dashboard app.omniatech.io and generate your private endpoint for the chain & network you want. Don’t forget to tick the Honeypot protection checkbox when customizing the subscription.
In case of detection of such a malicious activity like interacting with a honeypot ERC20 smart contract, the RPC will not process that transaction to protect your funds and will return a dedicated error code.
More information can be found at https://docs.omniatech.io/defi/honeypot-protection.